Risk Assessments
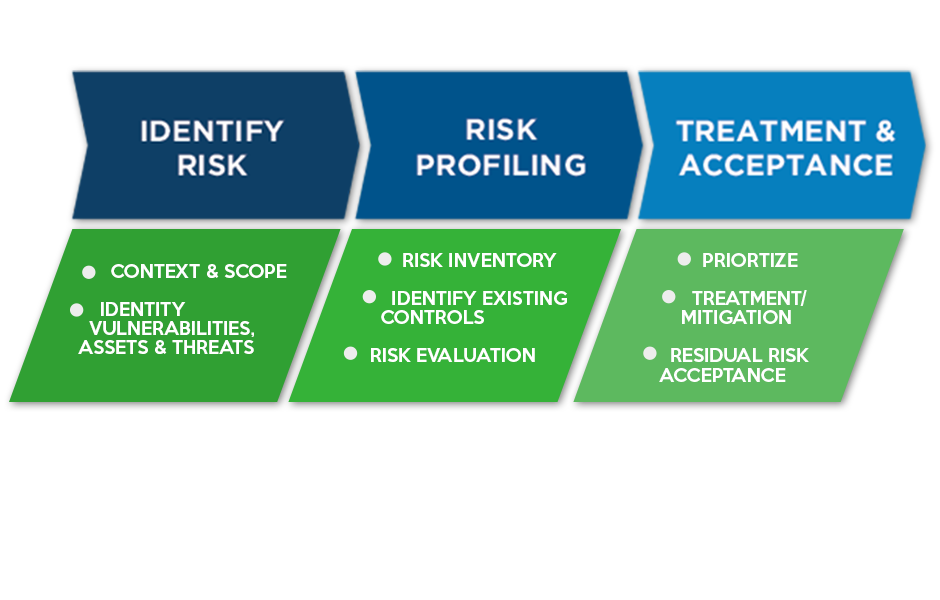
A security assessment is designed to evaluate the broad spectrum of your security controls against best practices and prominent security frameworks to determine how effectively those controls protect your organization from cyberattacks. Combined with clear guidance and recommendations to improve those controls, an assessment will help you establish a stronger security posture that is more effective in protecting your organization against cyber threats.
A security assessment also provides guidance on which specific risk factors to monitor over time to ensure that different courses of action can be taken if risks have reached an unacceptable level. Our experts chart best practices in security risk management for your industry.
Onexte Consulting risk assessment and management solutions use an optimal balance between people, process, and technology. Risk management is the key to a successful security strategy. Deliverables include comprehensive reporting that is valuable to both the technical and executive levels. For technical staff, we detail the immediate threats across your enterprise and recommend the appropriate responses. For executives, we clearly communicate systemic issues and solutions, prioritizing risk management strategies based on resources constraints and risk goals.
Let our experts show you how to:
- Obtain a list of information systems and assets
- Understand the threats to your assets
- Identify organizational vulnerabilities
- Identify technical vulnerabilities
- Document current controls and security processes
- Identify security requirements and considerations per regulatory requirements and industry standards
- Measure initial and residual compliance, reputation and direct loss risk
Vulnerability Assessment
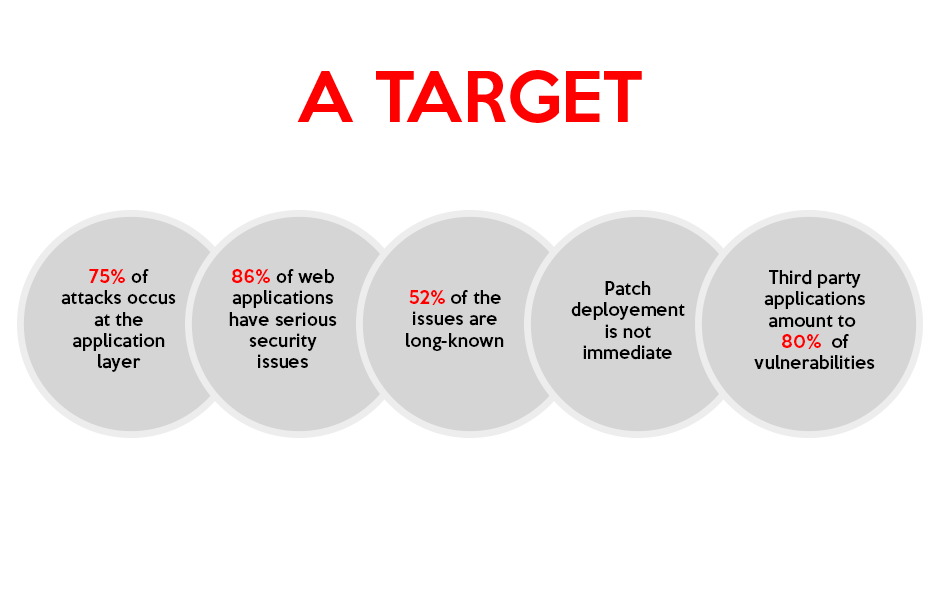
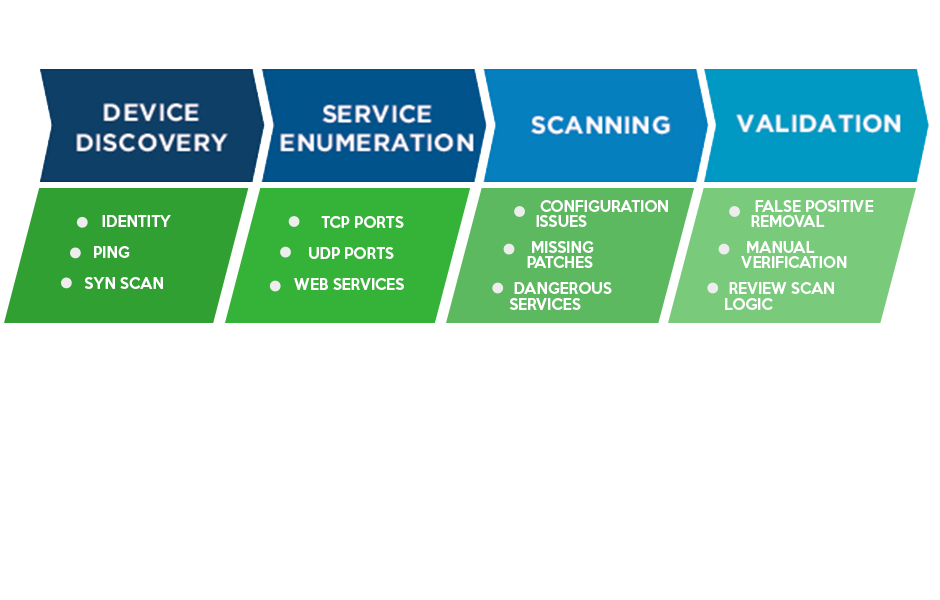
Vulnerability management is considered a security best practice defensive measure to protect against today’s real and potential threats. Onexte Consulting’s critical vulnerability assessment will identify vulnerabilities on your network devices, operating systems, web applications, databases and desktop applications. Onexte performs both external and internal vulnerability assessments.
As a critical tool for information security management, a vulnerability assessment can spot the weaknesses in your security defenses before an attacker can exploit them. Your adversaries are constantly striving to innovate their methods as they look for new ways to breach your defenses. A regular vulnerability assessment can help you be proactive in uncovering and addressing security flaws and refining your cyber security strategy to remediate them.
An effective vulnerability assessment requires proven methodologies created by security professionals with extensive and up-to-the-minute knowledge of the latest threats and the skills and technology available to mitigate them. Our approach to performing a vulnerability assessment exposes weaknesses in systems and identifies paths that are vulnerable to exploitation. Our mature methodology provides actionable recommendations to improve security in your systems. Working closely with our team, we can help you uncover vulnerabilities and identify steps to reduce risk within your business.
Our services include:
- Breach simulation, operating outside of traditional testing methodologies to simulate an attacker to uncover points of weakness
- Risk validation, where our experts attempt to breach the information security controls of your organization during a penetration test
- Security controls assessment to examine and assess various controls, technologies and procedures and identify points of failure
- Vulnerability discovery and threat modeling to identify, quantify and rank vulnerabilities in your systems
HITRUST Assessment
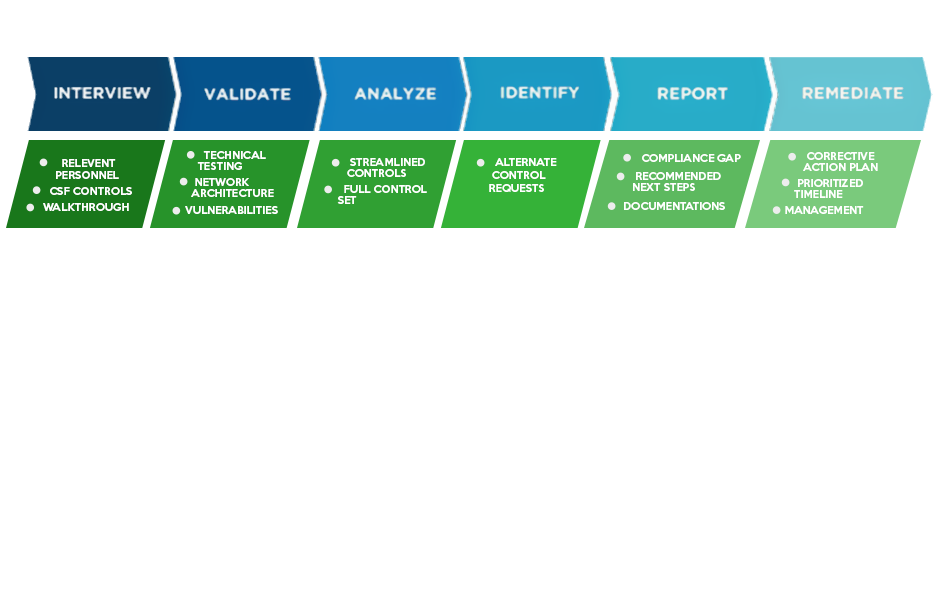
Developed in collaboration with healthcare and information security professionals, the HITRUST CSF is the most widely-adopted security framework in the U.S. healthcare industry. With the inclusion of federal and state regulations, standards and frameworks such as HIPAA, NIST, ISO and COBIT, the CSF is a comprehensive and flexible framework that remains sufficiently prescriptive in how control requirements can be scaled and designed for healthcare organizations of varying types and sizes. The HITRUST CSF is a standard which has been specifically tailored for the healthcare industry and incorporates both compliance and risk management principles.
Onexte performs HITRUST security assessments to evaluate the risks and compliance state of organizations which create, access, store or exchange sensitive and/or regulated healthcare data.
Onexte help healthcare organizations to:
Assess and Measure Gaps: HITRUST CSF assessment methodology performed by experienced, certified HITRUST CSF practitioners applied selectively to the HIPAA and HITECH Acts; prioritized and actionable recommendations; peer benchmarking.
Remediate and Enhance: Experienced, certified HITRUST CSF Practitioners, security program, policy, and procedures design, services, tools, and process implementation.
Execute and Monitor: HIPAA / HITECH compliant Log Monitoring, Log Management, Vulnerability Management and Security Device Management.
Demonstrate Compliance: Standard and customizable reporting, secure evidence repository for all HIPAA / HITECH compliance related assessments, results, and reports; integrated ticketing with assignment, tracking, and journaling.
Performing a HITRUST CSF assessment helps organizations align their controls, procedures, and policies to this framework. This ultimately helps them maintain compliance with industry standards and protect their most sensitive data. For organizations seeking to become fully certified, Onexte can assist them throughout the process.
Incident Response Assessment
Quick incident identification and remediation can reduce the financial impact to your organization. But, how do you know if your organization is prepared for an attack against a critical server? Do you have a documented and tested response plan? Does your Response Team know how to react to the attack?
Incidents differ and have varying potential impact. Onexte Consulting’s Incident Response and Readiness Assessment digs into your organization and leads a hands-on security evaluation comprised of four parts:
- Reviewing the current threat landscape
- Performing a targeted controls assessment to simulate an incident and evaluate the response
- Facilitating a tabletop exercise to review existing controls
- Help develop a CIRT (Computer Incident Response Team) and a documented incident response process
Our expert people and processes provide a thorough analysis detailing your incident response readiness and recommendations for improvement. The reality is no organization can ever be fully protected against potential attacks. But when they do occur, prepared organizations have a coordinated response with less loss and quicker recovery. Onexte Consulting can help you face advanced threats with confidence.
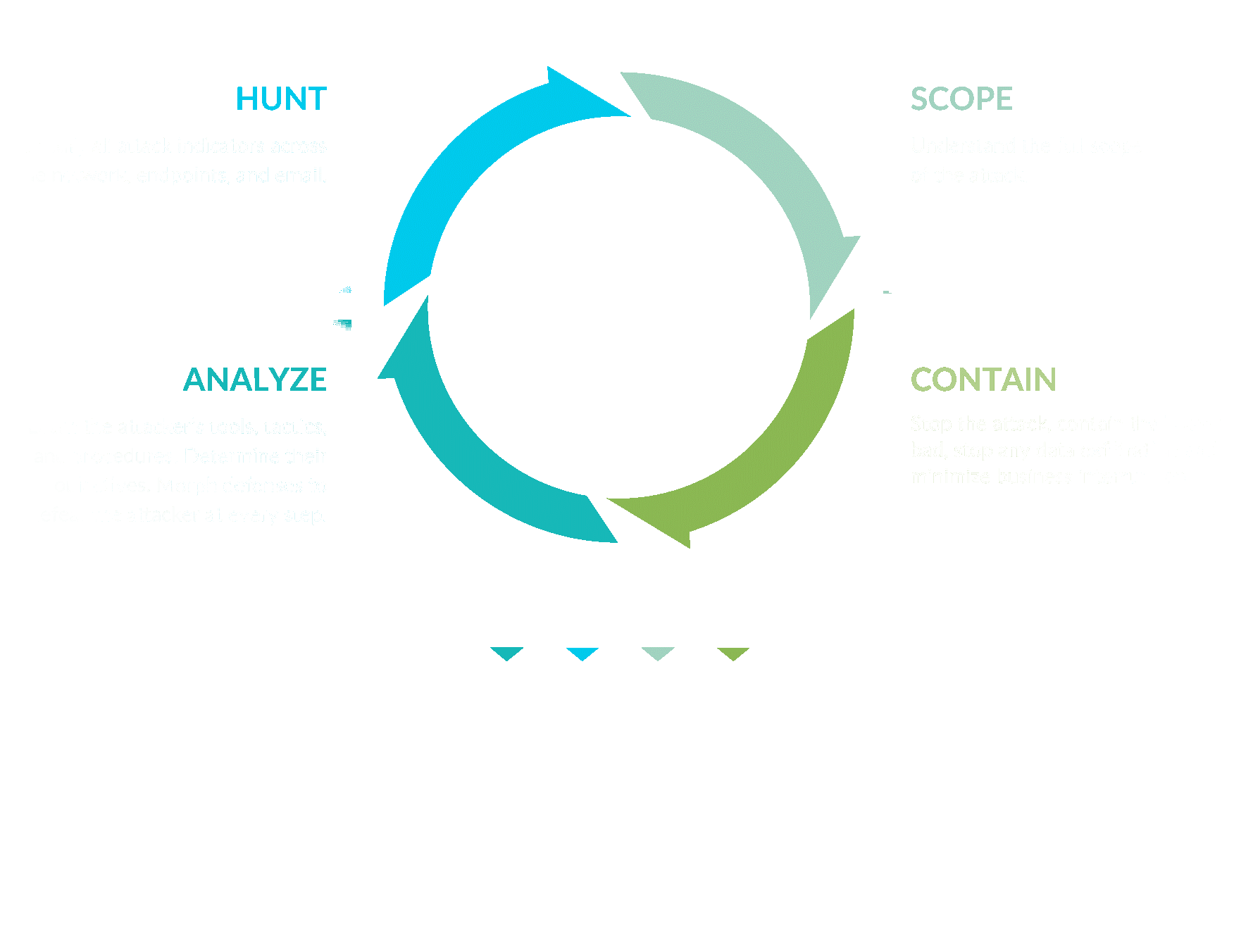
Onexte implements a comprehensive approach to incident response that enables us to address the full extent and impact of an attack. Our incident responders and malware reverse engineers identify every compromised system, account, and infected data set in order to quickly and completely remediate the incident. Most incident response firms simply identify and isolate compromised systems without addressing the full extent of the breach. This legacy approach to incident response often results in malicious artifacts and hidden intruders left behind and embedded in your network even after the visible breach has been addressed.